Quantum computers have promise to unleash a new era of computational power.
But as quantum computers advance, they could introduce new risks to our digital security, potentially break most modern cryptography, and render communications as insecure as if they weren't encoded at all.
For example, Rivest-Shamir-Adleman, a public key cryptosystem from 100 to 4,096 bits is widely used to protect everything from online purchases to work emails.
According to the 2021 Quantum Threat Timeline Report by Global Risk Institute, these computers will be able to break RSA-2048 within 15 years. The Cloud Security Alliance made a pessimistic estimate that Years to Quantum, also known as Y2Q or Q-Day, will arrive on April 14, 2030, although it did not state specific grounds.
That is when quantum computers render current encryption methods ineffective.
Computer scientists are actively exploring alternative algorithms to replace the vulnerable ones for a quantum-safe future. In August, the US National Institute of Standards and Technology released draft standards for three of its first four quantum-safe cryptographic algorithms.
This transition takes time, and the point here is planning is a more effective strategy than painstakingly reacting to threats.
Quantum computers have the potential to crack mathematical padlocks on encrypted data instantly, laying bare the world's secrets, because they could perform calculations out of reach for classical computers.
But quantum technology is still in its early stages and far too puny to defeat current strong security codes.
The question of when large-scale fault-tolerant quantum computers will be built is a complicated one. While in the past it was less clear that they are a physical possibility, many scientists now believe it to be merely a significant engineering challenge.
Governments, organizations and institutions, such as NATO and the White House recently started preparing for Y2Q, when more powerful machines are being regularly rolled out by IBM and Google.
Predicting the exact arrival of Y2Q is challenging due to the rapid pace of technological advancements.
However, it's not just a future problem. Securing encrypted traffic is a pressing problem today because data that requires long-term security could be at risk of "store today, crack later" attacks.
The goal is to develop systems that are secure against both quantum and classical computers, and can interoperate with existing communications protocols and networks.
The shift toward quantum-safe encryption, essential to ensure the security of sensitive data in the long term, will require significant investment of time and resources.
This presents an opportunity for organizations and institutions to focus on educating themselves and adapting their encryption systems to become quantum safe.
Historically, it has taken almost two decades to deploy a public key cryptography infrastructure. This provides a brief window to upgrade a digital infrastructure.
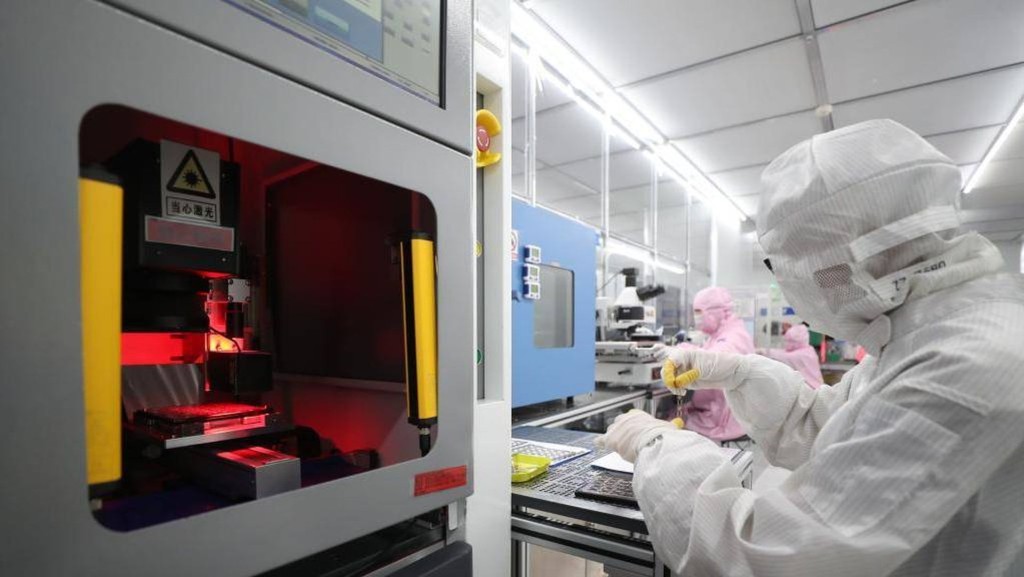
For example, British Telecom, alongside Toshiba, is developing a "world first" trial of a quantum secure communications network in London, with EY, a global professional services firm, becoming the first customer and HSBC recently joining.
It connects customers across London, helping them to secure the transmission of valuable data and sensitive information between locations using a technology called quantum key distribution.
QKD is a quantum-safe cryptography that leverages principles from quantum mechanics. It enables two parties to generate a shared random secret key known only to them and has a 'super-hearing' ability to detect someone eavesdropping on their conversation even from miles away.
By proactive planning with strategic actions now, we can ensure that our economies, communications, and sensitive data remain secure in a quantum future.
Let's prepare for the quantum threat before it arrives.
Dr Jolly Wong is a policy fellow at the Centre for Science and Policy, University of Cambridge
A quantum-safe communications network is undergoing testing in London.